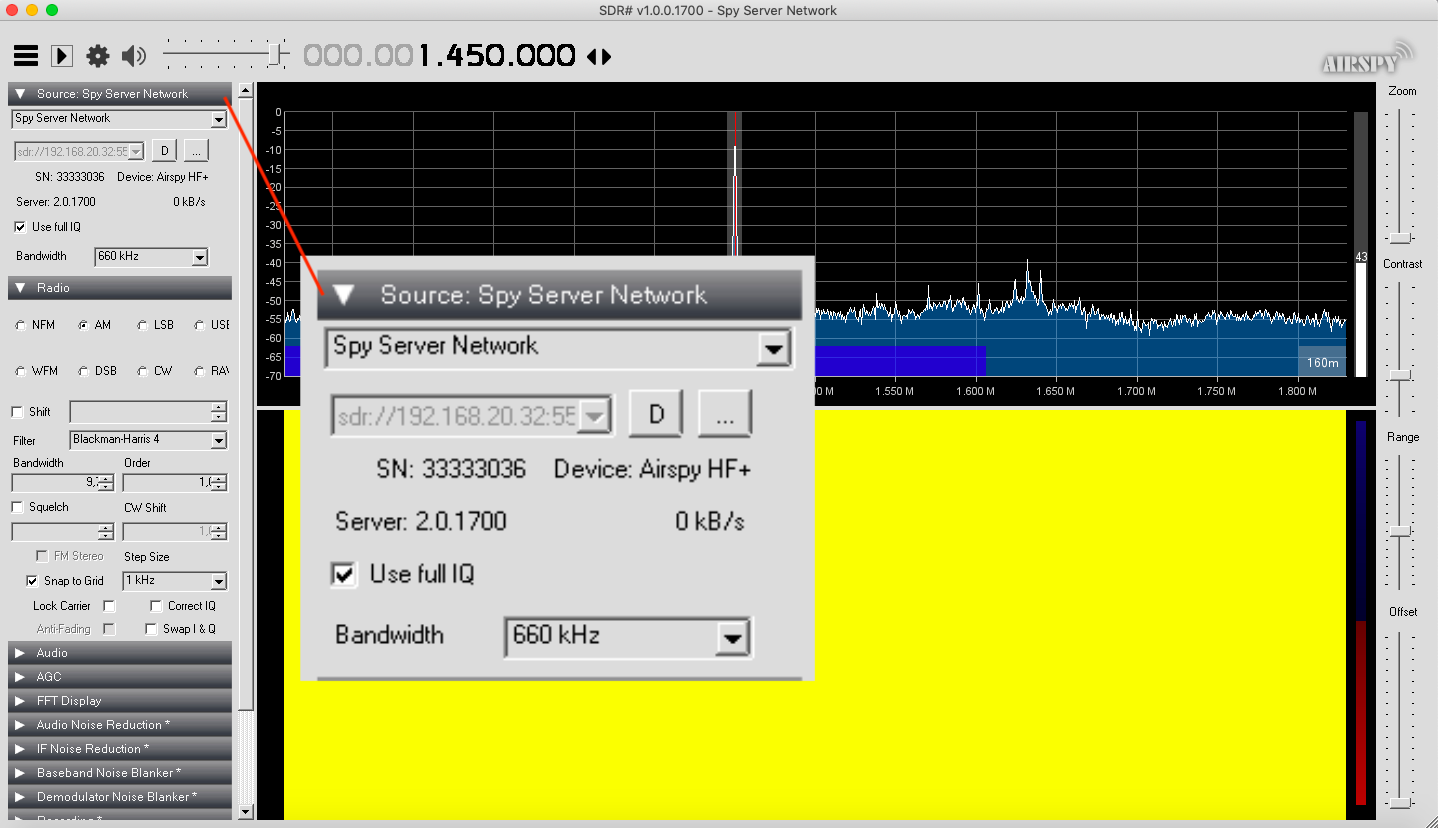
AirSpyHF+ on Spyserver on Raspberry Pi

What is a Spyserver and why do you NEED one? A spyserver takes an RTL-SDR software radio and allows it to be used over the network or controlled from the internet if you allow.
For this project I’m using the AirSpyHF+ ($199 USD). The AirSpyHF+ is probably the BEST HF SDR radio you can get. This project will let us operate from about 9kHz to about 31 MHz where AM radio, and Short Wave Radio reside.
On a fresh Raspberry Pi with Raspbian installed lets get started. Let’s install the libairspyhf driver. But first the prerequisites.
sudo apt-get install build-essential cmake libusb-1.0-0-dev pkg-config
I found that I had to add these dependencies otherwise the spyserver would just connect and then disconnect.
sudo apt-get install airspy libairspy0 libairspy-dev
Having these dependencies allows you to easily check your serial number for the conf file below by issuing the command:
airspyhf_info
Now build and install the driver:
mkdir airspy cd airspy wget https://github.com/airspy/airspyhf/archive/master.zip unzip master.zip cd airspyhf-master mkdir build cd build cmake ../ -DINSTALL_UDEV_RULES=ON make sudo make install sudo ldconfig
Okay now lets get the spyserver, unpack it, then run the program. Before you run the program below here is an example configuration file (spsyserver.config)
wget https://airspy.com/downloads/spyserver-arm32.tgz tar xzf spyserver-arm32.tgz ./spyserver spyserver.config
To edit the file be in the spyserver directory and issue a “sudo nano spyserver.config”
# SPY Server Configuration File # TCP Listener # bind_host = 0.0.0.0 bind_port = 5555-6666 # List Server in Airspy Directory # list_in_directory = 1 # Owner Name # For example: John Doe L8ZEE owner_name = John E. Hagensieker # Owner email # For example: owner_email = # Antenna # For example: Random Wire/Magnetic Loop/Mini-Whip/Inverted V/etc. antenna_type = dipole # Antenna Location # For example: 48.858332, 2.294560 antenna_location = 35.1085, 77.0441 # General Description # general_description = # User sessions # maximum_clients = 1 # Maximum session duration # In minutes. 0 for no limit # #maximum_session_duration = 30 # Allow clients to retune and change of gain of the device # allow_control = 1 # Device Type # Possible Values: # AirspyOne (R0, R2, Mini) # AirspyHF+ # RTL-SDR # Auto (Scans for the first available device) # device_type = AirspyHF+ # Device Serial Number as 64bit Hex # For example: 0xDD52D95C904534AD # A value of 0 will acquire the first available device. # device_serial = 0 # Device Sample Rate # Possible Values: # Airspy R0, R2 : 10000000 or 2500000 # Airspy Mini : 6000000 or 3000000 # Airspy HF+ : 768000 # RTL-SDR : 500000 to 3200000 # Comment to use the device's default # device_sample_rate = 768000 # Force 8bit Compression Mode # The 8bit Compression mode has proven sufficiently good for most streaming use cases. # Use it to same some internet bandwidth. # force_8bit = 1 # Maximum Bandwidth # Limits the maximum IQ bandwidth the clients can set # Recommended value for WFM is 200000 # Recommended value for narrow band modes is 15000 # #maximum_bandwidth = 15000 # FFT Frames Per Second # fft_fps = 10 # FFT Bins # Bins = 2^fft_bin_bits # fft_bin_bits = 16 # Initial Center Frequency # initial_frequency = 14500000 # Minimum Tunable Frequency # Comment if using the device default # #minimum_frequency = 0 # Maximum Tunable Frequency # Comment if using the device default # #maximum_frequency = 35000000 # Frequency Correction in PPB # #frequency_correction_ppb = 0 # Initial Gain # #initial_gain = 10 # RTL-SDR Sampling mode # Quadrature = 0, # Direct Sampling I Branch = 1 # Direct Sampling Q Branch = 2 #rtl_sampling_mode = 2 # Converter Offset # Set to -120000000 to enable the SpyVerter offset #converter_offset = -120000000 # Bias-Tee # For AirspyOne only - Useful for LNA's and SpyVerter enable_bias_tee = 0 # Buffer Size (in milliseconds) # buffer_size_ms = 50 # Buffer Count # buffer_count = 10
Now lets make it run all the time.
sudo apt-get install supervisor
Now go to the spyserver directory and make a script file
cd spyserver sudo nano spyserver.sh
Paste this in and hit CTL + X then Y to save
#!/bin/bash /home/pi/spyserver/spyserver /home/pi/spyserver/spyserver.config
Now make it executable
sudo chmod +x spyserver.sh
Now we go to the supervisorord.conf file.
sudo nano /etc/supervisor/supervisord.conf
Paste this in:
[program:spyserver] command=/home/pi/spyserver/spyserver.sh autostart=true autorestart=true stderr_logfile=/var/log/long.err.log stdout_logfile=/var/log/long.out.log
Now if you reboot spyserver will start and it will restart if it crashes or start at boot time.
I use a VPN to get inside my network but if you want to access spyserver from the internet you will have to port forward on your router the IP address of the Raspberry Pi on port 5555.
Then you can connect to the spyserver from wherever.

what IP address should I use for the Spy server and do I set it in the Spyserver config? Can I use another port instead of 5555?
you can use the IP address of the machine or 127.0.0.1 and yes you can change the port to whatever unused port you want.
To check the serial number, firmware version, etc., he correct command is airspyhf_info, NOT airspy_info.
John,
Thanks for the step-by-step,,,
David Lee thanks for the airspyhf_info command vs. airspy_info
I ran lsusb on my Raspi4 with the W3JDS Ham radio 2.0 build…
Sadly my new AirspyHF+ Discovery only shows up on the lsusb report but not on the airspyhf_info commands.
I feel I am close but missing something.
$ lsusb
Bus 003 Device 001: ID 1d6b:0002 Linux Foundation 2.0 root hub
Bus 002 Device 001: ID 1d6b:0003 Linux Foundation 3.0 root hub
Bus 001 Device 014: ID 093a:2510 Pixart Imaging, Inc. Optical Mouse
Bus 001 Device 013: ID 04d9:0006 Holtek Semiconductor, Inc.
Bus 001 Device 012: ID 05e3:0610 Genesys Logic, Inc. 4-port hub
Bus 001 Device 015: ID 03eb:800c Atmel Corp. Airspy HF+
Bus 001 Device 002: ID 2109:3431 VIA Labs, Inc. Hub
Bus 001 Device 001: ID 1d6b:0002 Linux Foundation 2.0 root hub
The new Airspy works perfectly under Windows with SDR# but I am hoping to make it work with the RPi4 for portability etc…
What program are you trying to use it with? Did you install rtl-sdr?
John,
Today it seems I can see the device so I can proceed with the rest of the configuration etc.
pi@raspberrypi:~ $ airspyhf_info
AirSpy HF library version: 1.6.8
S/N: 0xDD52D780A1224ACC
Part ID: 0x00000001
Firmware Version: R3.0.6-BB
Available sample rates: 768 kS/s 384 kS/s 256 kS/s 192 kS/s
I should be able to finish the connection to RTL-SDR or other client that can talk to this server.
Thanks for the quick reply.
Cheers,
Glen AD8CR
Hi Glen
I have exactly same problem like you. which version of raspberry have you preinstalled? i usted raspberry PI OS Lite 32bit and made the steps in the tutorial here. but i always got the error ->
root@raspberrypi:/home/pi# airspy_info
airspy_lib_version: 1.0.9
airspy_open() board 1 failed: AIRSPY_ERROR_NOT_FOUND (-5)
but lsusb see’s my airspy hf device ->
root@raspberrypi:/home/pi# lsusb
Bus 002 Device 001: ID 1d6b:0003 Linux Foundation 3.0 root hub
Bus 001 Device 003: ID 046d:c52b Logitech, Inc. Unifying Receiver
Bus 001 Device 009: ID 03eb:800c Atmel Corp. Airspy HF+
Bus 001 Device 002: ID 2109:3431 VIA Labs, Inc. Hub
Bus 001 Device 001: ID 1d6b:0002 Linux Foundation 2.0 root hub
root@raspberrypi:/home/pi#
with windows – same as in your case – the device works perfect (but i want the server on a raspi…)
Which steps have you done to proceed configuration?
John,
All is working! I logged in from my Windows PC running SDR# and was able to tune the AirspyHF+ Discovery hosted on my RPi4. Curiously it only worked if I put the IP address of the host RPi4 into the config file. The IP was 192.168.1.135. I would have expected the client SDR# machine to be routed to this IP if I left it as 127.0.0.1 localhost within the config file.
Just when I thought I knew networking….
Either way, I have a path forward with this compact platform. I can put it in the yard with a nice big antenna and not hassle with pulling coax into the house. Less wires more smiles.
Cheers,
Glen AD8CR
My HF+ Discovery arrived today. I have no driver for Android apps, etc. so it is useless except for the bright LED! $184?? I have a strong desire to see something like the spyserver ported to termux on android so I can run my Airspy HF+ Discovery on my Android phone. But termux is not Linux exactly so I’d have to learn many details about compililng/linking on it. Or perhaps get someone like Martin Marinov to make a driver for SDRTouch. I don’t think I can do the pi thing, that is too new/technical.
Phil
Tested the Discovery at public library with sdr#, was disappointed somewhat, no WWV even, only noise.
Used AndroNix to install Ubuntu on my Android phone and then compiled airspyhf driver, installed spyserver (the pi arm32 version) itself, then ran QuestaSDR. Everything tested out except that libusb is incompatible/doesn’t function under Termux, and termux-usb hangs. So it’s close but needs a libusb patched like in SDR Touch, Martin Marinov did this with rtl_tcp_andro-:
“This is a modification of rtl_tcp and libusb-1.0 for running on Android (also works on other Linux based systems)”
“Files modified in libusb-1.0 to create libusb-andro: core.c, libusb.h and libusbi.h – to header for and implementation of the open2 function which takes an already open file descriptor linux_usbfs.c – to create a libusb handle from the fd”
It appears to be a job for an Android guru. The spyserver would need to use the open2 function. But I don’t see any source code for it! So at this point I am still defeated.
Pingback: Einsatz meines Raspberry Pi 3 Model B für Amateurfunkzwecke – DL1HBT
Great detail, thank you, fixed my issues getting a HF+ to work on a Pi with airspy spyserver.
strace -f -o spyserver.trace ./spyserver showed me the driver issue, which then lead me here.
Your instructions state that after the command “sudo apt-get install airspy libairspy0 libairspy-dev
“, it is possible to execute the command “airspyhf-info”. I found that this wasn’t the case. I had to do a “sudo apt get install airspyhf” first.
Thanks for the otherwise excellent instructions. This finally got me over the hump of using my DiscoveryHF+ remotely.